I’ve periodically seen (and heard about) spam emails which attempt to blackmail the recipient. They’re an interesting phenomenon, and tend to use the form of starting out with “you’ve been hacked and your password is [common password]”. I’ve seen some variations, like “password”, “a1b2c3”. I forget the name for that but it’s an interesting technique where by being specific you throw out most of your potential audience but seem to have information you shouldn’t to the small bit that remains.
One such story I’ve heard was about a con artist who selected 4096 names and addresses from the phone book, then sent each of them a letter introducing himself and giving a free tip. He picked a stock and to half said that it was going to go up, to the other half that it was going to go down. The stock then went up or down, and he threw out the half for whom his prediction was wrong. He then did the same thing to the remaining 2048 people, dividing them in two again. Finally he was down to only 4 people but from their perspective he had made 10 accurate predictions in a row! It couldn’t be chance!
Obviously this is less sophisticated, but it’s interesting for other reasons, too, so I’m going to go through it and point them out.
Subject: Frauders known your old passwrd (a1b2c3). Password mut be changed.
I find it very interesting that it starts out as if it’s from someone in a position of authority, which I suspect is just for the obvious reason of getting someone to read it. I’ve also heard that spammers don’t spend much time on plausibility because only very gullible people will fall for the scams anyway. Curious start, though.
Hello!
I have bad news for you. 19/09/2018 – on this day I hacked your OS and got full access to your account [redacted]. On this day your account [redacted] has password: a1b2c3
The friendliness is interesting, given that this is an attempt at blackmail. Anyway, we see the use of the common password which will be right for only some people.
So, you can change the password, yes.. But my malware intercepts it every time.
How I made it: In the software of the router, through which you went online, was a vulnerability. I just hacked this router and placed my malicious code on it. When you went online, my trojan was installed on the OS of your device.
This starts off plausible, but after that (mostly) only works in movies. Hacking a router is a start, but you can’t just “install a trojan”. Trojans are programs which do something real but also have a malicious payload. Routers don’t automatically install software onto client machines every time those machines go online.
Worse, it’s been a while since almost all web traffic has switched to SSL, which, granted, a router can try doing a man-in-the-middle attack on, but that’s not easy since these days browsers make it hard to trust self-signed certificates. Again, we see a surface veneer of plausibility. Much like science fiction.
After that, I made a full dump of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
This is pretty boiler-plate for these sorts of emails. Kind of a standard “I have power over you”. Now is when it gets interesting:
A month ago, I wanted to lock your device and ask for a not big amount of btc to unlock.
It’s interesting that it’s using the generic “device”. The English in this one is fairly good; enough that I wonder if the occasional “foreign speaker” mistakes are a put-on in order to disguise where this stays generic.
But I looked at the sites that you regularly visit, and I was shocked by what I saw!!! I’m talk you about sites for adults. I want to say – you are a BIG pervert. Your fantasy is shifted far away from the normal course!
I’ve got to say that I love the idea that the criminal who was planning to break your computer and ransom your data was utterly shocked by pornography. I think it makes a certain amount of sense in terms of trying to set the tone, since the blackmail that is to follow depends upon a sense of shame in the victim.
And I got an idea….
I made a screenshot of the adult sites where you have fun (do you understand what it is about, huh?). After that, I made a screenshot of your joys (using the camera of your device) and glued them together.
Turned out amazing! You are so spectacular!
The faux-friendly tone is quite interesting, especially when coupled with a sort of flattery. I wonder if the idea behind the flattery is to pretend to knowledge that the story would have be true to have, or something else. Possibly it’s just to try to amplify the sense of shame in the victim.
I’m know that you would not like to show these screenshots to your friends, relatives or colleagues. I think $719 is a very, very small amount for my silence.
And here we finally get to the blackmail. (Incidentally, “I’m know” is an odd mistake. And someone who doesn’t speak English natively seems unlikely to use “huh?” so correctly in the preceding paragraph. And they got the second sentence correct including punctuation.)
Also curious that there’s no reference to having looked at the victim’s online banking and saw that he can easily afford this.
Besides, I have been spying on you for so long, having spent a lot of time!
This may be the part I find most interesting—the blackmailer is basically appealing to a living wage theory of the time-value of work. He’s put so much time in, he deserves a lot of money!
Pay ONLY in Bitcoins!
My BTC wallet: 1J5SXcupgaq2tUas5S7wVtf7evJp6YC3LJ
You do not know how to use bitcoins? Enter a query in any search engine: “how to replenish btc wallet”. It’s extremely easy
Curious that they include instructions to search rather than actual instructions. On the other hand, writing good instructions is hard work and the willingness to do hard work is not why criminals get into crime, by and large. (note: I didn’t redact or change the bitcoin wallet because, well, why should I?)
For this payment I give you two days (48 hours). As soon as this letter is opened, the timer will work.
Now we’re basically in the realm of complete fantasy. Email clients don’t send read-receipts any more and haven’t for a long time. Granted, the blackmailer has (in theory) installed a trojan on the victim’s computer, but in that case why not say that he’s watching via the webcam? Of course, that might prompt the victim to take immediate action which would make him find out it’s a hoax.
It’s also curious that it’s 48 hours. It’s short enough one can’t put it off indefinitely, but it’s also plenty long enough to do some basic searching and find out that this is a common hoax. And to install anti-virus software and find out that there are no trojans. (Though there’s some mention of this later.)
I think the idea is that there’s supposed to be a relatively short timer which will cause the victim to panic and act before thinking, but why two whole days rather than, say, 60 minutes or 4 hours or something short enough that there isn’t much time for non-compliance?
After payment, my virus and dirty screenshots with your enjoys will be self-destruct automatically. If I do not receive from you the specified amount, then your device will be locked, and all your contacts will receive a screenshots with your “enjoys”
I think that the automatic self-destruction of the evidence is a nice touch. It suggests that one doesn’t need to trust the villain to obtain the desired result, though about a quarter of a second of thinking about it would make such assurance worthless (if for no other reason than the villain could be lying about the automatic self-destruct). Presumably, though, they’ve discarded the quick witted as potential victims anyway.
I hope you understand your situation.
– Do not try to find and destroy my virus! (All your data, files and screenshots is already uploaded to a remote server)
– Do not try to contact me (you yourself will see that this is impossible, the sender address is automatically generated)
– Various security services will not help you; formatting a disk or destroying a device will not help, since your data is already on a remote server.
This is an interesting attempt to head off common responses. Of course, since this is a hoax, the real intent is to prevent the victim from finding out that there’s no virus. Still, it’s curious that it suggests alternative courses of action. I suppose they will arise anyway since everyone’s first thought will be how to get out of this situation without paying, so shaping the thoughts in a direction that’s unlikely to work is to the blackmailer’s benefit.
P.S. You are not my single victim. so, I guarantee you that I will not disturb you again after payment!
Interesting that the blackmailer takes thought for the possibility that he’s lying, or will be back for more, and tries to head this off. I wonder if it’s partially the result of blackmailers never stopping being such a common idea in murder mysteries? Could that popular form of entertainment have made life slightly harder for real-life blackmailers? It’s an interesting idea.
This is the word of honor hacker
I also ask you to regularly update your antiviruses in the future. This way you will no longer fall into a similar situation.
Do not hold evil! I just do my job.
Good luck.
This sign-off is very curious. Presumably the blackmailer doesn’t actually care what the victim thinks of him—and has no hope of the victim thinking of him in a friendly way, anyway—so it must serve some other purpose. Making the hoax seem more real? I remember reading C.S. Lewis commenting on how the art of including irrelevant details to make a narration seem more real was part of what distinguished the modern novel from more ancient tales; could this art be used in hoaxing in this manner? Or possibly it’s akin to the stage magician’s art of redirection? If the blackmailer can get his victim to focus on whether or not the blackmailer has a black heart he will forget to ask whether the blackmailer actually has the evidence he claims? It would, after all, be very easy to include a screenshot from the claimed video as proof, were the blackmailer actually telling the truth.
Of course, it’s easy to read too much into such a scam. There’s no proof that I know of that anyone has actually fallen for it. The victims of such a scam are not likely to come forth and tell the world they’ve been scammed since it would be admitting exactly what they wish to conceal, and for no gain since the odds of recovering money sent to an anonymous bitcoin wallet are not high. And without knowing how successful the scam is, there’s little we can tell from it besides what a scammer—who possibly has no experience—thinks is likely to be a good scam.
That said, I still find it interesting from the perspective of someone who writes murder mysteries since those tend to be stories that involve at least one amateur—the murderer. But there are often more; red herrings are almost always, by definition, people who are not practiced. After all, if they were skilled, they’d be the murderer, not a red herring.
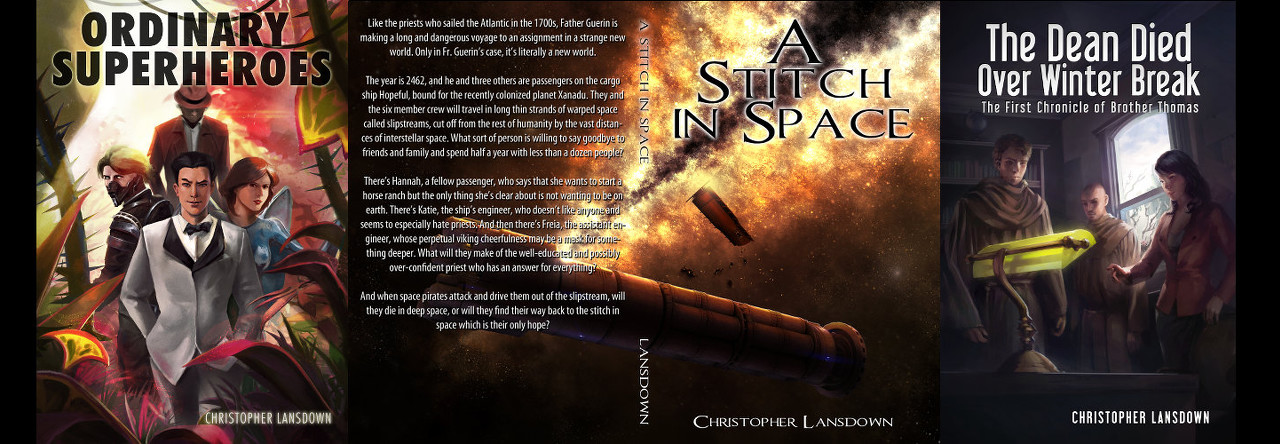
Discover more from Chris Lansdown
Subscribe to get the latest posts sent to your email.
I think they’re using lists of passwords from hacked sites. They’re either relying on people reusing passwords all over the web or a real password from somewhere adds a touch of verisimilitude. At least sometimes, common passwords is certainly a possibility. A while back, somebody worked up the nerve to ask me whether he should worry about one of these he’d received and the password in it was one he knew he’d used before but it wasn’t a common one.
48 hours might be more effective in the early days of something like this. If you’re one of the first to get one there might not be anything on the web about it being a scam yet. Maybe somebody’s first reaction would be “to hell with them, I’ll take my chances” but then they’ve got a couple of days to let worry gnaw at them.
LikeLike
Interesting. That would make sense if they use those old hacked lists so that they have a password and an email together.
LikeLike
Also, good point with the extra time allowing the worry to gnaw on them.
LikeLike